CloudFabrix AIOps 360 solution can ingest alerts, events, metrics and from various monitoring tools to perform event correlation, alert noise reduction and enable incident resolution acceleration. Learn more about CloudFabrix AIOps 360
In this blog I will cover Zabbix integration aspects with our AIOps 360 solution. Zabbix is one of the popular open source monitoring platforms used by many enterprises and MSPs, including some of our customers. Zabbix can monitor most applications and infrastructure and it is very extensible and programmable as well. Learn more about Zabbix
Why Integrate
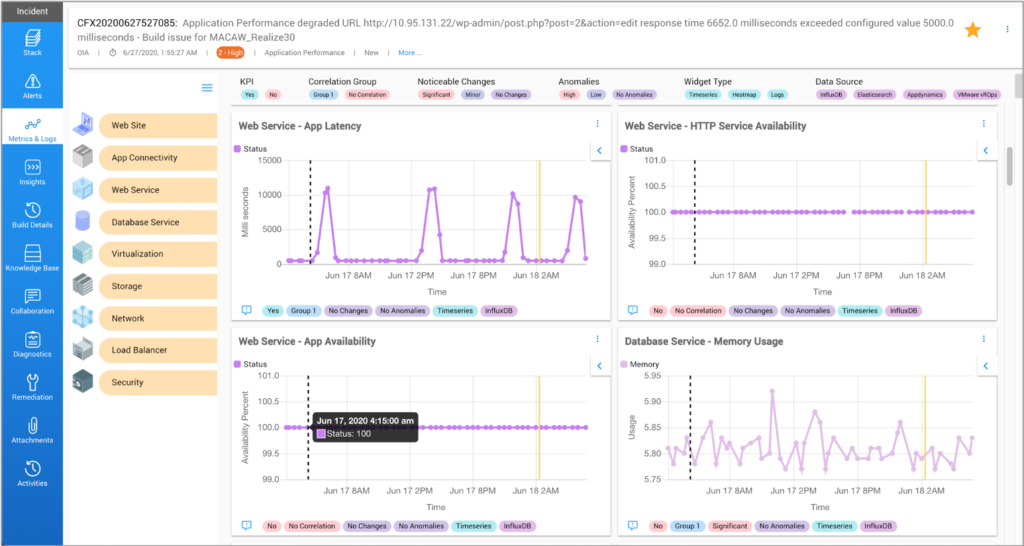
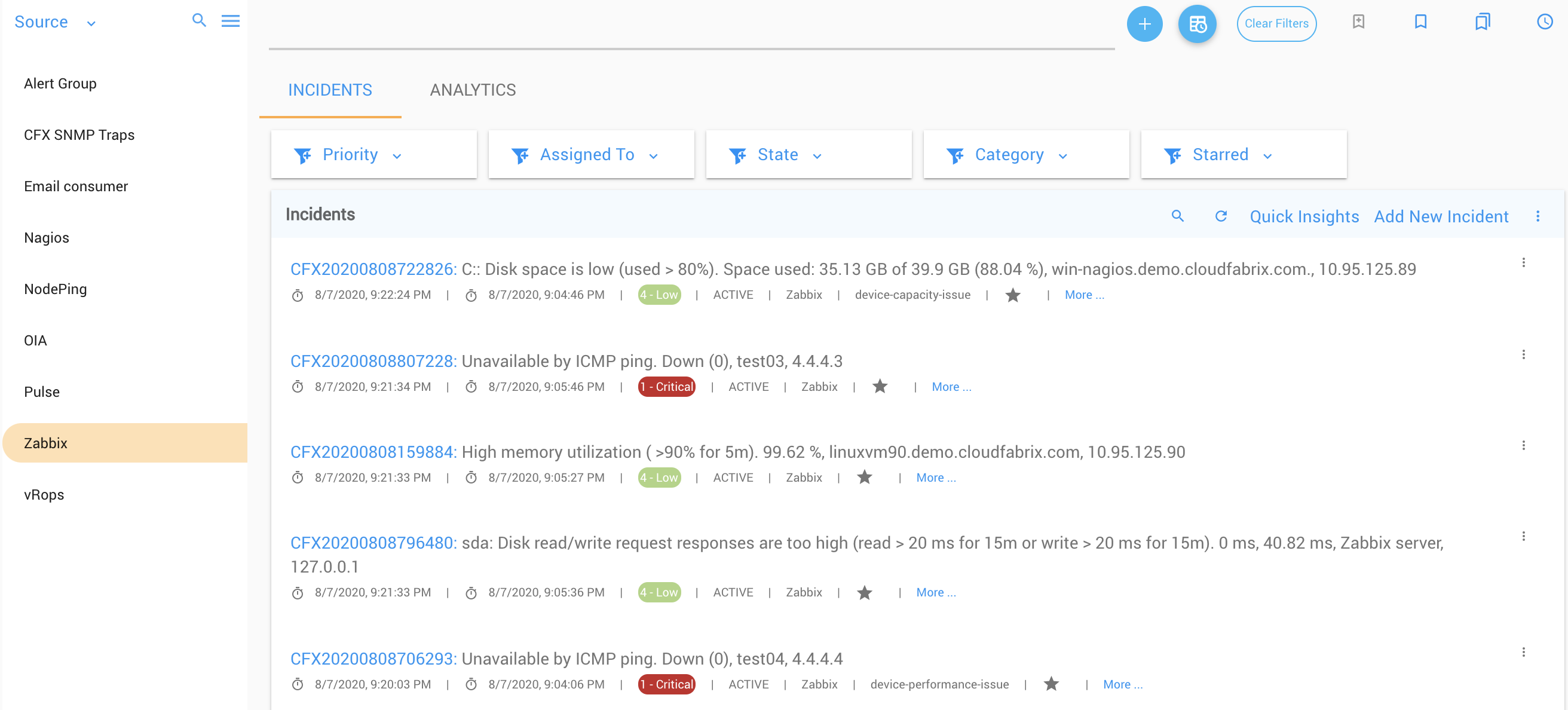
With this integration, customers will be able to view, correlate Zabbix events/alerts with alerts coming from other domain-specific monitoring tools (application, cloud, network or virtual infra). This gives customers a single pane alert visibility, analytics and ML driven correlation and reduces the number of tickets or incidents in the ITSM tool (ex: ServiceNow, PagerDuty, Jira ServiceDesk etc.). It will also enable customers to see time series m
etrics data dynamically retrieved from Zabbix in presented in our single pane incident triage dashboard, where Zabbix metrics are juxtaposed along with all additional incident relevant metrics (time-aware, context-aware, CI-aware) pulled from other domain-specific monitoring tools.
What it will Give
- Single pane alert console
- Alert, event correlation
- Accelerating incident resolution
- Predictive insights
What is Ingested from Zabbix
- Zabbix alerts, events
- Zabbix alert rule name (i.e template name)
- Zabbix time series metrics
- Zabbix CI to host group mapping
- Zabbix metadata tags (environment, location etc. that admin may have setup per host)
How it Works
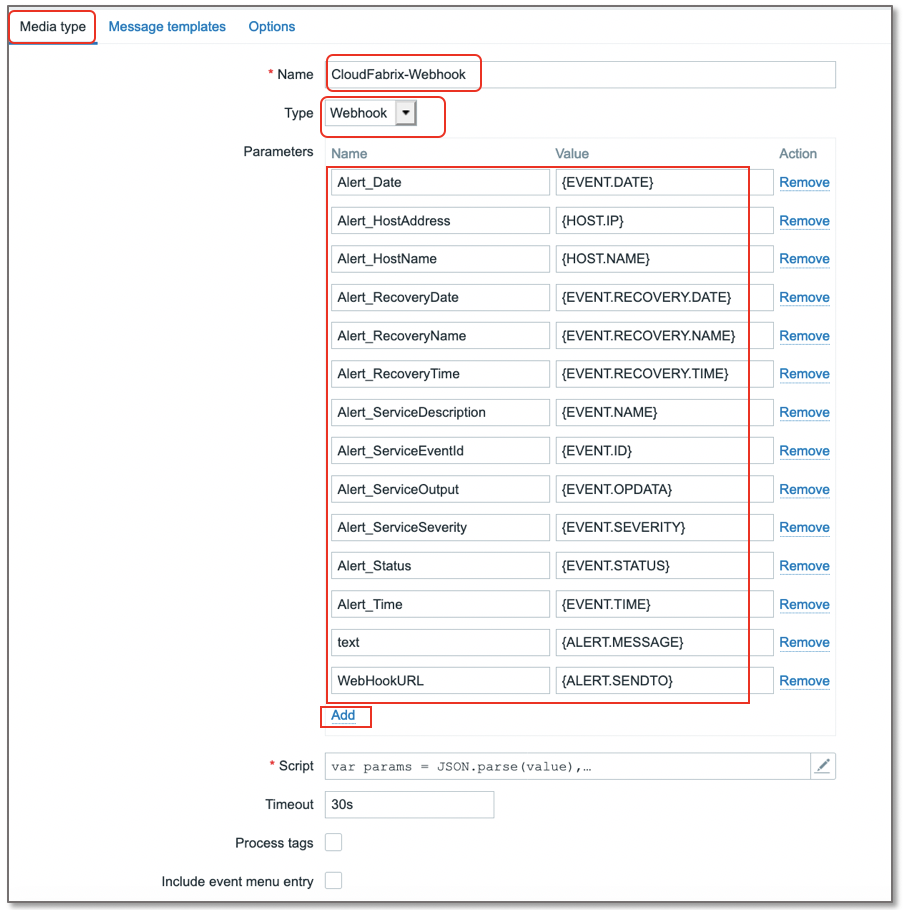
Integration leverages webhooks based mechanism to automatically send alerts from Zabbix to CFX. This happens as and when alerts arise (new, update, clear) and there is no need to perform polling. Initially, an integration endpoint has to be crated in CFX that gives out a unique Webhook URL, which will then be used in Zabbix as a destination webhook to send alerts/events to. In Zabbix, webhook payload can be customized by including few important attributes from event table, alert table and host table (ex: EVENT.NAME, EVENT.OPDATA, ALERT.MESSAGE, HOST.NAME, HOST.IP etc.). These are all mapped to certain variable CFX defined variables in the webhook payload. When alert is received by CFX tool, it will have data populated based on the payload defined in webhook setting. CFX will perform rest of the processing (enrichment, correlation etc.)
Key Integration Steps/Summary
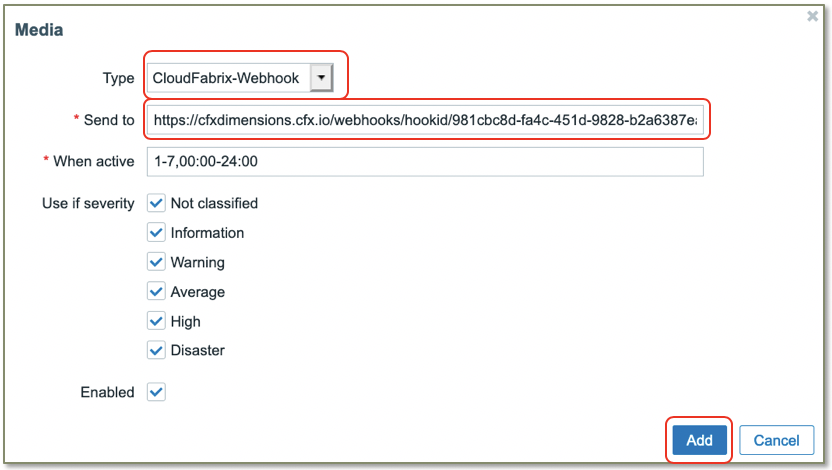
- In CFX: create Integration endpoint and get unique webhook URL to be used in Zabbix and optionally setup basic authentication.
- In Zabbix: create a new webhook Media Type
- Customize payload using variables and JavaScript
- Update the message template (how alert messages will appear)
- Reuse or create a new alert notification user that has visibility for all host groups
- In the Media for above notification user, select webhook created above and use the webhook URL from CFX endpoint as the destination URL. Enable for all times.
This will take care of receiving alerts, events from Zabbix into CFX AIOps platform. Receiving of time series metrics will be covered in a later blog. Details integration instructions are covered in CloudFabrix documentation site.